Walkera quadcopter firmware hacking
Wednesday, March 25, 2015
Walkera produces realy fine and popular quadcopters. They are targeted to people who want to have fun flying. Just buy one of these RTF (ready to fly, no assembly or soldering required) models and start. That’s perfectly OK. But for me I always want to know whats going on inside a device. Especially a quadcopter. I own a few models and also some Walkera ones. A Hoten-X and a Ladybird. After analyzing the firmware update process of the Walkera Devo-7 transmitter and the Hoten-X (RX2635H) and Ladybird (RX2634H) receivers in another post, I now analyzed the receiver and its firmware.
This post is part of a series
- Flashing new Firmware to Walkera RX/TX without UP02
- Decrypting receiver firmware (this post)
- Walkera receiver components
- Hello World firmware for the RX2635H board
- Serial port and external 16MHz oscillator
- Using the ITG-3205 mems gyro
- Walkera UP02 software clone: UP42
- Walkera RX2635H as generic development board?
- Walkera USB port
- Walkera + Arduino = Walkino
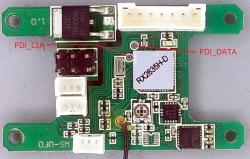
In most Walkera receivers an Atmel XMEGA (Hoten-X and Ladybird both use a XMEGA32 AU4) is used. So this provides the first hint on architecture. The XMEGA uses the new PDI (Programming and Debugging Interface) instead of the well known ISCP interface of other Atmel microcontrollers. Fortunately the used PDI pins (PDI_CLK and PDI_DATA) are both available on the receiver PCB. So I just connected my AVRISP mkII programmer (which supports PDI for the XMEGA’s) and tried to read out the firmware.
Too bad!!! Walkera has disabled the feature to read back the flash!
So I needed another way to analyze the firmware. Fortunately the firmware can be updated using the integrated boot loader (see this post). Firmware updates for both receivers are available on Walkeras homepage. After downloading I first opend them with a HEX editor and looked for some human readable text strings or other known values like reset or interrupt vector jumps that can be found in the XMEGA datasheet and AVR instruction set manual.
Again - NOPE!!!
So there must be some form of security mechanism (encryption) applied. Using the Hoten-X firmware I started with the simplest form of encryption - the XOR. As the integrated boot loader has to perform the process of decrypting the uploaded firmware before writing the clear bytes to the flash during the update process, it could only be a very simple mechanism as there is not much room for complex algorithms like certificate based ones in the boot loader.
The interrupt jump table at the beginning of the file is more or less empty resulting in a repeating pattern of jump statements. By calculating the difference from the bytes in the encrypted firmware with the jump opcode value a part of the key could be restored repeating after 16 bytes. So the key was 16 bytes long. An XOR with the partial key reveals the final information needed to get the whole key. At the end of the Hoten-X firmware update file a more or less human readable text apears.
This text is the same information you can read from the boot loader by using the I (Information) command described here. So this way the rest of the key could be easily calculated. The same mechanism also works for the Ladybird receiver. It looks like that every Walkera receiver model has its own “unique” 16 byte key. These are the keys I have discovered so far:
- Ladybird (RX2634H) = D0 94 3F 8C 29 76 15 D8 20 40 E3 27 45 D8 48 AD
- Hoten-X (RX2635H) = 8E 50 01 66 52 6E 7B D7 EE C8 5C 7A C0 5A D7 92
- V120D02S (RX2636) = 89 C7 26 B4 DF 65 26 A1 B7 CA 5F 0C 70 33 B9 BA
With this information it’s now possible to start writing custom firmwares for this receivers by just reversing the process of decryption. After compiling a new firmware just XOR the binary with the key and upload it to the receiver. And it is also possible to always go back to the original firmware.
For XORing on Windows or Linux you can use this simple tool http://aluigi.altervista.org/mytoolz/xor.zip which works and has source code included.
On Windows enter:
xor.exe hoten_x_fw.bin hoten_x_fw_decrypted.bin 0x8E500166526E7BD7EEC85C7AC05AD792
to decrypt e.g. the Hoten-X firmware.